If you integrate your Enterprise applications with Azure AD, you may want allow your users to invite external users in a secure manner, without enabling guest access to any other resources, or having to involve admins every time a guest needs to be added.
Microsoft document how to allow your users to manage guest access here:
https://docs.microsoft.com/en-us/azure/active-directory/b2b/what-is-b2b
So there are 2 ways to do this, either you let Admins add your B2B users, or you can let your own users do this. This article focuses on the latter, enabling your users to add guests, whilst doing so in a secure manner. The Microsoft article above does not discuss how to securely enable guest access in the first place, so this is the focus of this post.
Note that if you just want to control access to Teams, SharePoint, OneDrive and Office 365 groups, all of these are controlled separately and you don’t need to do follow this first section. See the end of this post for more detail.
Securing guest access to applications
As already mentioned, Admins can add guests to the directory, so if you want complete control of guest access then do not turn on the settings below. Once an admin has added a guest, users can then invite the guests to various resources as required.
Steps to allow Guests to invite users to specific applications are documented here, I am going to assume you have done this:
https://docs.microsoft.com/en-us/azure/active-directory/b2b/add-users-information-worker
However, these steps are not enough on their own, once you have allowed users to manage access to an individual application, you need to follow the steps below to complete the process. Note that these settings are tenant wide, so will also apply to other applications, and the domain restrictions will also apply to Teams or SharePoint, so bear that in mind before you start restricting guests to specific domains.
Guest invitation settings
If you want to allow collaboration without requiring the intervention of Admins, and want to enable guest access outside of Teams or SharePoint e.g. to B2B applications that you have integrated with Azure AD, you need to enable users to invite guests at the Tenant level:
Enable users to add guests on the tenant
- Go to the Office 365 Portal at https://portal.office.com
- Settings -> Security & privacy -> Sharing
- Click Edit and then allow users to add new guests
Enable users to add guests in Azure AD
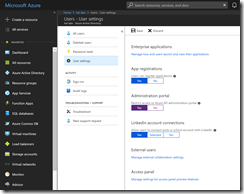
Note that the same setting can be accessed in Azure AD, so alternatively can be set here:
- Go to the Azure Portal at https://portal.azure.com, then open the Azure Active Directory blade
- Click Users under Manage
- Click User Settings, and then Manage external collaboration settings:
- Set Members can invite to Yes (you should generally set Guests can invite as No)
Now this is rather open by default, so we can then restrict the types of guests as follows:
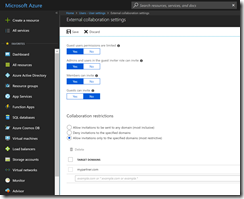
Setting Collaboration restrictions
Now, choose how restrictive you want to be by setting the collaboration restrictions to one of the options:
- Allow invitations to be sent to any domain
- Deny invitations to the specified domain
- Allow invitations only to the specified domain
If you need users to be able to invite guests, you can use a whitelist to ensure that they can only invite users at from domains of your choosing. So you could add in the domains of your partners here, to ensure that users can collaborate with your partners, but not other external users.
If possible, use the last option and enter the domains of your partners. Note that this will also affect other areas e.g. SharePoint and Teams, so you should add the domains of all of your partners here. Note that this setting will prevent even an Admin from adding a guest from an unauthorised domain directly to Azure AD, but if this is required you could briefly add a domain to the list.
Users can then add guests using the Access Panel at myapps.microsoft.com, but only the domains which are allowed.
Note: The inviting user must have an Azure AD Premium license for the manage app option to appear. Usually this is via an EMS license.
Putting it all together
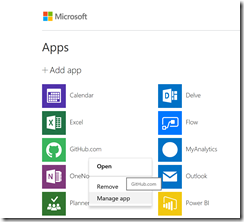
Now users can invite guests to the app that they have been assigned as an owner:
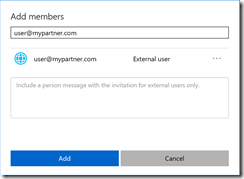
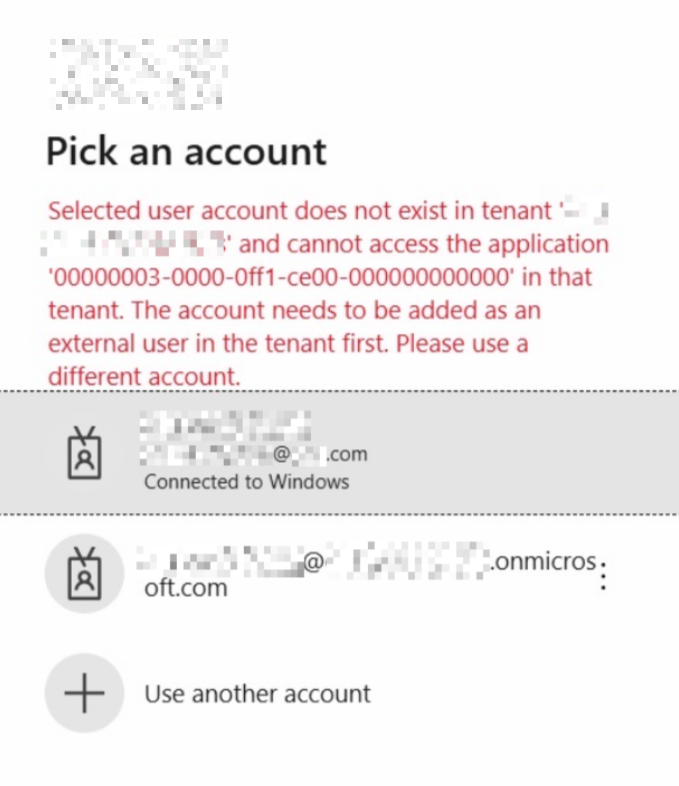
If another domain is tried, they will get an error:

This will also apply to Teams:

Restrict access to the Azure AD portal
- Go to portal.azure.com
- Click Users under Manage
- Click User Settings
- Under Administration porta, click Yes – Restrict access to Azure AD administration portal
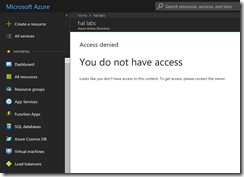
If you do this then users will be unable to use Azure AD from the portal:
Other guest settings
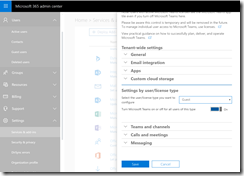
Teams
If you only need to enable Guest access for Teams collaboration, you just need to go to portal.office.com, then Settings > Services & add-ins > Microsoft Teams > Settings by user/license type
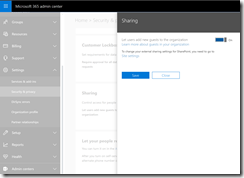
SharePoint
SharePoint and OneDrive guest access is also controlled separately in the SharePoint Admin center:
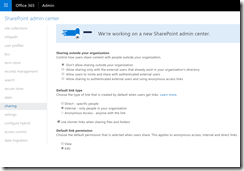
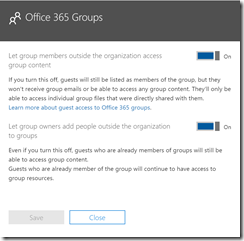
Office 365 Groups
You may want to turn off the following switches under Admin Center > Home > Services & add-ins > Office 365 Groups:
- Let group members outside the organization access group content
- Let group owners add people outside the organization to groups