Office 365 can enable new ways of collaborating with suppliers and business partners. However, it is important to understand the security implications of this, and you will probably want to lock this down initially.
By default, any user can invite external third parties into your Office 365 tenant, where they may have access your sensitive data. So in order to secure your data and applications, you should change the default settings.
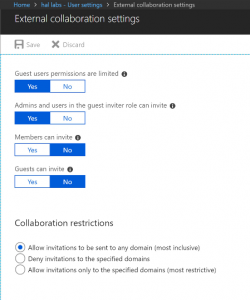
External Collaboration Settings
By default, normal users can invite guest to Azure AD. So Members can invite should be turned off, and you should also turn off Guests can invite.
Note that users can still invite guests if an Admin has added them to Azure AD already. So if an Admin has added guests to Azure AD directly, they could then be added to any app by any user, so this should be avoided. To change the collaboration settings:
- Navigate to https://portal.azure.com
- Open Azure Active Directory
- Click User Settings
- Click Manage external collaboration settings, under External users at the bottom
Both bottom options below should be set to No:
Now you may still need guests to have access to individual apps. This can still be done either by Admins, or delegated to business users.
Inviting guests to your directory
- You can invite guest users to the directory, to a group, or to an application.
- The invited user’s account is added to Azure Active Directory (Azure AD), with a user type of Guest
- The guest then has to redeem their invitation to gain access
- You can either send the guest user a direct link to a shared app, or the guest user can click the redemption URL in the invitation email.
Inviting Guests to apps:
- Either an admin can add guests to Azure AD, and then application owners can invite users to individual apps
- Or, applications can be setup as self-service, so that application owners can add guests directly. This is the option we should use.
1. Add guest users to the Azure Active Directory (admin)
After a guest user has been added to the directory in Azure AD, an application owner can send the guest user a direct link to the app they want to share.
This is not normally a good idea, since the guests could then be added to other apps, even if collaboration settings have been disabled
2. Add guest users to an individual application (admin)
This could be done if you do not want business users themselves to be able to invite guests for any reason, i.e. you want absolute control.
- Sign in to the Azure portal as an Azure AD administrator.
- In the navigation pane, select Azure Active Directory.
- Under Manage, select Enterprise applications > All applications.
- Select the application to which you want to add guest users.
- On the application’s dashboard, select Total Users to open the Users and groups pane.
- Select Add user.
- Under Add Assignment, select User and groups.
3. Business users adding guests to an application
First, the application has to be configured for self-service:
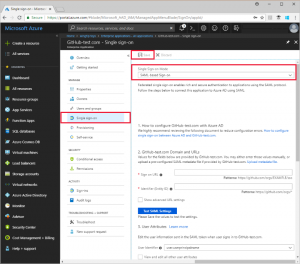
Then a group can be assigned as an owner as follows (see https://docs.microsoft.com/en-us/azure/active-directory/b2b/add-users-information-worker#prerequisites for details):
- Enable self-service group management for your tenant
- Create a group to assign to the app and make the user an owner (note that the group has to be in AAD not on premise, since they need to able to manage group membership)
- Configure the app for self-service and assign the group to the app
The users can then invite users to the app:
- Open the Access Panel by going to https://myapps.microsoft.com
- Point to the app, select the ellipses (…), and then select Manage app.
Note: The inviting user must have an Azure AD Premium license for the manage app option to appear. Usually this is via an EMS license.
B2B Guest Inviter role
There is also a Guest Invitier role, however you generally don’t want to use this, since this will effectively allow them to invite anyone to anything the same as an Admin (as it says above, Admin and users in the guest inviter role can invite).
https://docs.microsoft.com/en-us/azure/active-directory/b2b/add-users-administrator