Update: This information is now out of date. Baseline policies are being deprecated, we highly recommend using Security Defaults instead of manually enabling MFA if you do not have Azure AD Premium, see https://cloudrun.co.uk/office365/increase-your-office-365-security-for-free-with-security-defaults-for-admins/
How to secure your Office 365 tenant with multi-factor authentication using Azure MFA. Security of your Office 365 tenant is paramount. This is the minimum you should do in order to improve security and prevent unauthorised access. What we are going to do is:
-
-
- Enable MFA for your admin accounts
- Enable MFA for all other users (requires Azure AD Premium).
- Add a trusted location, so that you don’t have to use MFA when in your office or other location with a static public IP address.
-
Note: if you don’t have Azure AD Premium as part of EMS (E3) or another license, you will only be able to enable the MFA for Admins policy, and you will not be able to set locations or other advanced options. You can however still manually turn on MFA for all users.
Prerequisites
First, check that you have modern authentication enabled for Exchange Online. Without this, you will be unable to connect Outlook to Exchange Online with an MFA enabled account:
Check the status:
Get-OrganizationConfig | select *OAuth*
If this is set to false, enable it:
Set-OrganizationConfig -OAuth2ClientProfileEnabled:$true
Configure Tenant MFA Settings
These settings are used to define e.g. which authentication methods are available, and the MFA trusted IPs. This applies to Azure AD MFA only (i.e. not if you are using a third party MFA service with Azure AD or ADFS). You will need at least one Azure AD Premium license to do this, either through EMS or another license, or you can just create a free trial to do this as a one off.
- In the Azure AD Portal, navigate to Azure Active Directory > Conditional Access > Named locations > Configure MFA trusted IPs
- App passwords: Allow users to create app passwords to sign in to non-browser apps
- Trusted IPs: Skip multi-factor authentication for requests from federated users on my intranet
- Verification options: Select as required:
- Call to phone
- Text message to phone
- Notification through mobile app
- Verification code from mobile app or hardware token
- All users to remember multi-factor authentication on devices they trust, days before a device must re-authenticate: Unticked (or set this as required).
Now, if any of your global admin accounts are used by normal users e.g. for email, you may also want to change the duration that passwords can be saved for, otherwise they will have to reauthenticate in e.g. Outlook every 14 days by default.
Note that the setting: ‘Skip multi-factor authentication for requests from federated users on my intranet’ can be used when you just want to skip MFA for any users who are authenticated through ADFS internally, this can be useful when you use a cloud based web proxy service and cannot specify locations by IP address. However note that this setting does nothing on its own, you are simply saying that internal ADFS authenticated users are trusted. You can then specify trusted locations in a conditional access policy.
Enable MFA for Global Admins
It is recommended that you have dedicated accounts with Global Admin rights. Don’t assign the role to normal user accounts, by creating separate accounts you improve security since you aren’t accessing the tenant all the time with your privileged account. Your admin accounts don’t have to have a license assigned.
Enabling this policy will be that global admins will be required to use MFA from any location, even if they are inside your network. This is so that an internal network compromise could not then allow indirect admin level access to Office 365. This is the effective baseline MFA policy and will apply regardless of other policies.
Note that there is now a default policy in Office 365 in order to enable MFA for Global Admins, so this is very easy to implement:
-
-
- In the Azure AD Portal, navigate to Azure Active Directory > Conditional Access
- Select: Baseline policy: Require MFA for admins
- Enable policy: Use policy immediately.
-
Note that this will apply even if your admins come from trusted locations.
Enable MFA for all users
Whilst you can enable this on a per-user basis, the best way to do this is using a conditional access policy. That way you can be sure no users have been missed, and you don’t have to worry about enabling it for new users.
Using a conditional access policy (Azure AD Premium required)
Create a conditional access policy in Azure AD as follows:
-
-
- In the Azure AD Portal, navigate to Azure Active Directory > Conditional Access
- New Policy: Name: Internal Users MFA Policy
- Users and Groups: Include: All Users
- Cloud apps: All cloud apps
- Conditions: Locations: Include: All locations. Exclude: All trusted locations
- Access controls: Grant access: Require multi-factor authentication
- Enable policy: On
-
Manually (any license)
If you don’t have an Azure AD Premium license, you can still enable MFA by going to Settings > Services & add-ins > Azure multi-factor authentication, then enable it for your users.
-
-
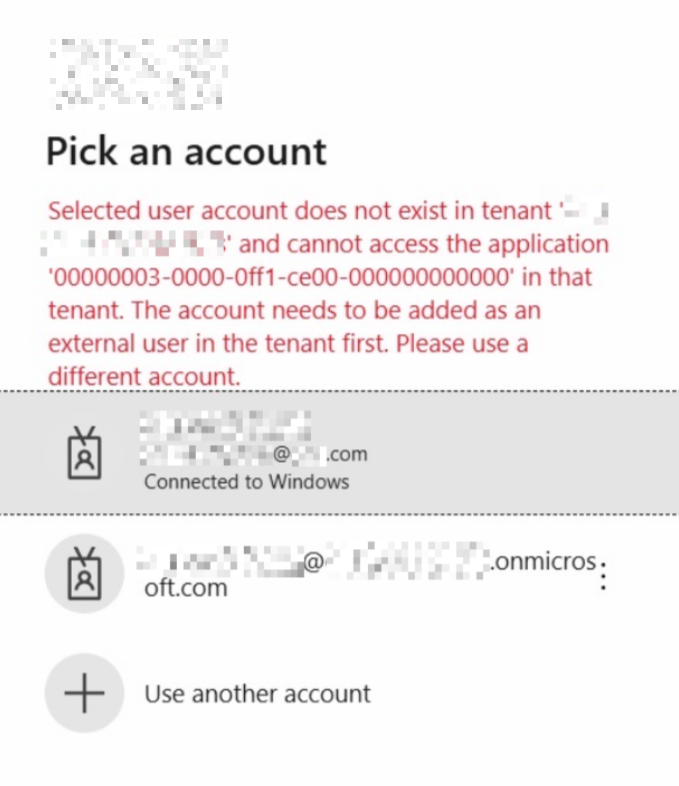
- Login to portal.office.com with your admin account
- Click Settings > Services & add-ins > Azure multi-factor authentication
- Click Manage multi-factor authentication
- Click at the top to select and enable MFA for all users
-
Now, by default users will be able to register with the following options:
Add alternative authentication phone numbers
You should note that all of these methods will probably use the same mobile phone. Therefore once set up, you should instruct users to go back and add their Office and Home phone, in case for any reason they do not have their mobile phone. Otherwise, they may be unable to login to their account.
Instruct users to do this as follows:
-
-
- Login to https://www.office.com/
- Click on the username in the top right, the My account
- Security & Privacy
- Additional security verification, Update your phone numbers used for account security.
- Add Office phone and Alternative authentication phone, when you are next at those locations.
-
Note: Using the link https://aka.ms/MFASetup will take you straight to the page below.
See https://docs.microsoft.com/en-us/azure/active-directory/user-help/multi-factor-authentication-end-user-manage-settings for more information.